A post takes seconds to upload, but the consequences can last for years. That is the strange part of online life: something casual, emotional, funny, or impulsive can become part of your long-term record. That matters because employers, training programs, scholarship reviewers, volunteer coordinators, and community organizations may all see some version of your online presence before they ever meet you.
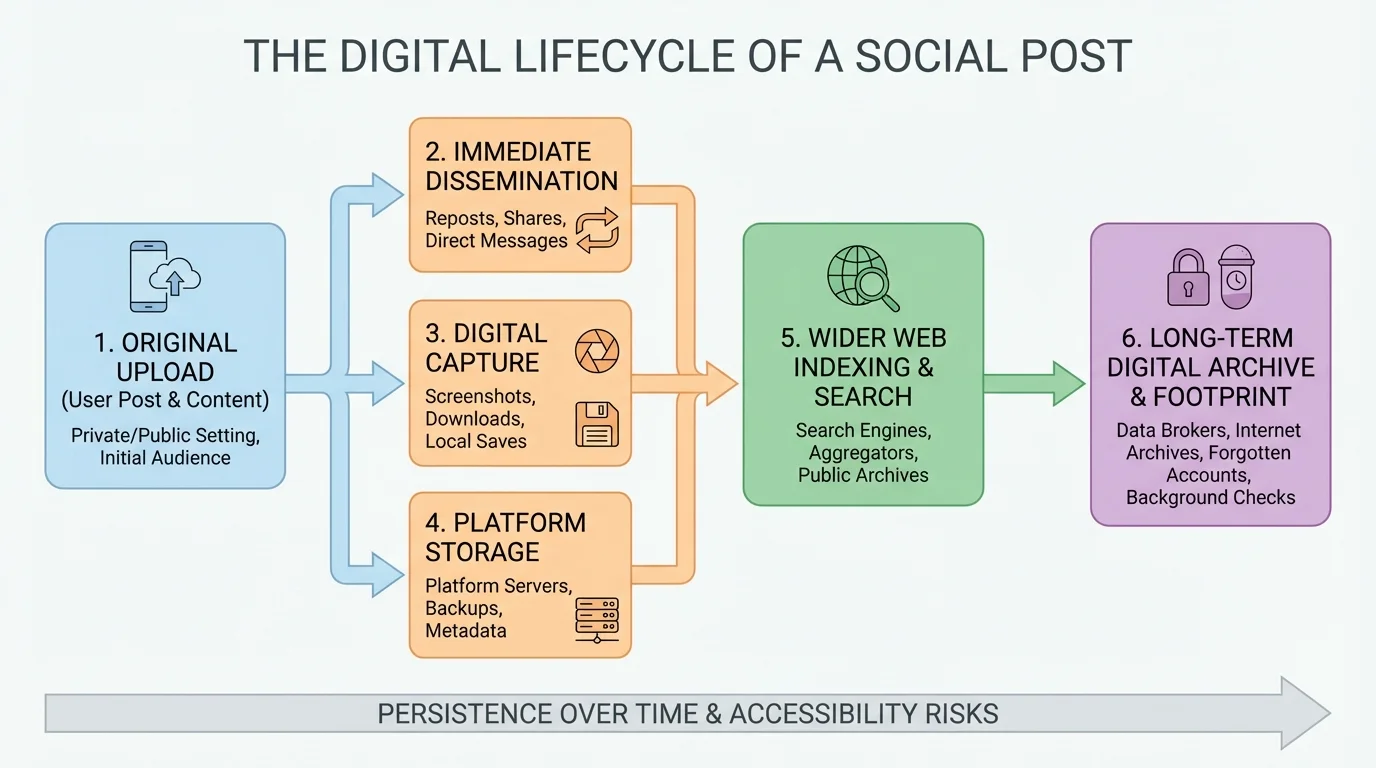
Your digital footprint is the trail of information connected to you online, and it is larger than most people realize. It includes what you post publicly, what friends tag you in, what accounts you follow, what comments you leave, what apps collect about you, and what data companies store. As [Figure 1] shows, even a post meant for a small audience can move far beyond its original setting through screenshots, reposts, search results, and saved copies.
This matters because the internet is not just a place for the present moment. It is also a system built for storage, copying, and searching. Deleting something later may reduce harm, but it does not guarantee that the content is truly gone. Someone may have downloaded it, captured it in a screenshot, or forwarded it to others. A joke made at midnight can become a problem during a job application six months later.
Long-term digital risk is not only about embarrassing photos or offensive language. It also includes patterns. If your online history repeatedly shows cruelty, dishonesty, reckless behavior, or poor judgment, people may assume those patterns reflect your real-life character. Fair or unfair, online patterns influence trust.
Long-term digital risk is the chance that something you do online today could harm your safety, privacy, reputation, relationships, education, or career in the future. Digital responsibility means acting online in ways that protect yourself and respect other people.
On the other hand, your digital life can also work in your favor. A thoughtful profile, respectful comments, creative projects, volunteer updates, or examples of leadership can help people see you as capable and reliable. Digital citizenship is not just about avoiding mistakes. It is also about making choices that support the life you want.
Whether you plan to work right after high school, attend college, start a training program, freelance, or combine several paths, your online presence can affect opportunities. Employers often review public profiles. Colleges and scholarship committees may see public content too. They may not know your whole story, so they often make fast judgments based on what is easy to find.
A single issue is not always what closes a door. More often, it is the overall impression: Are you respectful? Do you seem dependable? Do you handle disagreement well? Do you show responsibility? If your profile contains hate speech, threats, harassment, illegal behavior, or repeated insults, people may decide you are too risky to represent their workplace or program.
There is also a less obvious problem: content that is not harmful but still looks careless. For example, posting publicly about skipping obligations, mocking customers, sharing private workplace information from a part-time job, or bragging about breaking rules can make supervisors wonder whether they can trust you. In education, posting someone else's work as your own can raise concerns about academic honesty even outside a formal class setting.
Real-world scenario: two applicants, different outcomes
Both students apply for the same paid internship.
Step 1: The supervisor searches both names online.
Student A has a basic public profile, a few respectful posts, and a link to design work. Student B has several public arguments, reposts private screenshots of other people, and jokes about being impossible to work with.
Step 2: The supervisor compares risk.
Even if Student B has talent, the supervisor may decide the risk of drama or poor judgment is too high.
Step 3: The decision reflects trust, not just skill.
Digital behavior becomes part of how adults evaluate reliability, professionalism, and maturity.
Your online presence can also become a portfolio. If you create art, write clearly, edit videos, build code projects, run a small business page, organize a local fundraiser, or explain ideas well online, those things can support your future. The goal is not to become fake or overly polished. The goal is to make sure your public identity does not contradict your real goals.
Think of your online presence as having two sides: a private side for trusted people and a public side that may be seen by strangers. Strong digital responsibility means you manage that boundary on purpose instead of leaving it to chance.
Privacy problems are not always dramatic at first. Sometimes they begin with small habits: posting your location in real time, using the same password everywhere, sharing personal details in bios, clicking rushed links, or trusting messages just because they sound urgent. Strong privacy settings help, but privacy is really a combination of settings, habits, and judgment. Layered protection matters, and [Figure 2] illustrates the basic parts of a safer setup.
One major risk is identity theft, when someone uses your personal information to pretend to be you, open accounts, scam others, or access your money and records. Young people are sometimes targeted because they may not check credit reports or account activity often, which means fraud can go unnoticed longer.
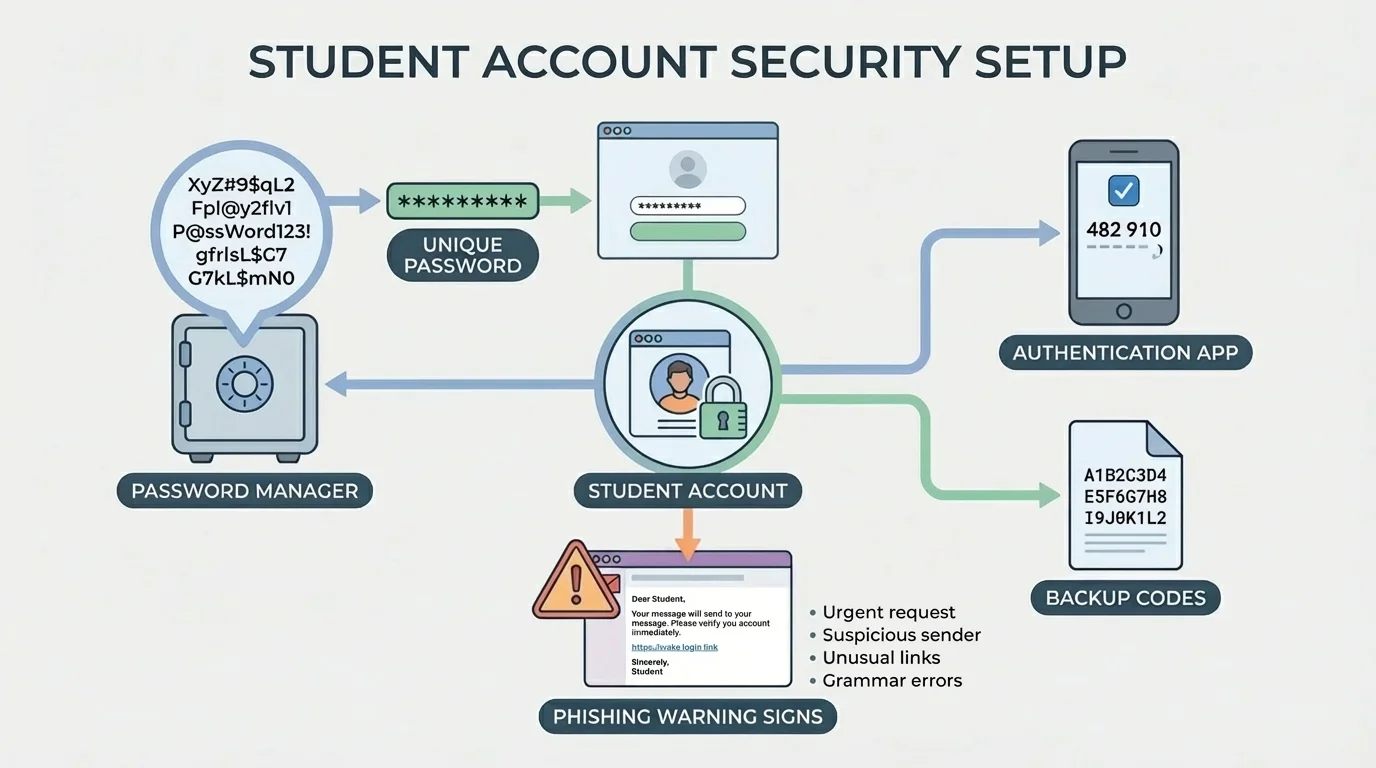
Another major risk is account takeover. If one password is used on multiple sites and one site gets breached, a criminal may try that same password everywhere else. That is why unique passwords matter. A password manager can generate and store strong passwords so you do not have to memorize all of them.
You should also turn on multifactor authentication whenever possible. This adds another step, such as an authentication app or security code, so a stolen password alone is not enough. That extra step can be the difference between a minor scare and a serious account loss.
Watch out for phishing, which is any message designed to trick you into giving up information, money, or account access. Phishing often creates pressure: "Your account will be locked," "You have won a prize," or "Click now to fix a problem." Slow down. Check the sender. Go directly to the official site or app instead of using the message link. If someone pushes urgency, that is a reason to become more careful, not less.
Think in layers, not single fixes
Digital protection works best when you stack habits together: unique passwords, multifactor authentication, software updates, limited public sharing, careful clicking, and backup recovery options. No single tool makes you safe by itself, but several good habits together reduce your risk a lot.
Location sharing deserves special attention. Posting where you are in real time can reveal routines, school-related schedules, work shifts, gym habits, or when your home is empty. A better habit is to share photos after you leave a location, not while you are still there.
The same idea applies to personal details. Your birthday, phone number, address, full legal name, family names, answers to security questions, and photos of documents all have value to scammers. Before posting or sending personal information, ask yourself whether the other person actually needs it.
Most digital mistakes happen fast. You react, tap, and move on. A better approach is to use a quick risk assessment before you post, click, forward, or reply. As [Figure 3] shows, a simple decision path can help you slow down just enough to avoid preventable problems.
Use this five-question check:
Question 1: Is it true? If you are not sure, do not share it as fact.
Question 2: Is it yours to share? Private screenshots, personal stories, and other people's photos usually require permission.
Question 3: Could it harm your future? Picture a supervisor, coach, scholarship reviewer, family member, or community leader seeing it later.
Question 4: Does it expose personal information? Look for names, addresses, schedules, usernames, account details, or location clues.
Question 5: Are you emotional right now? Anger, jealousy, embarrassment, and loneliness can push you to post things you will not stand by later.
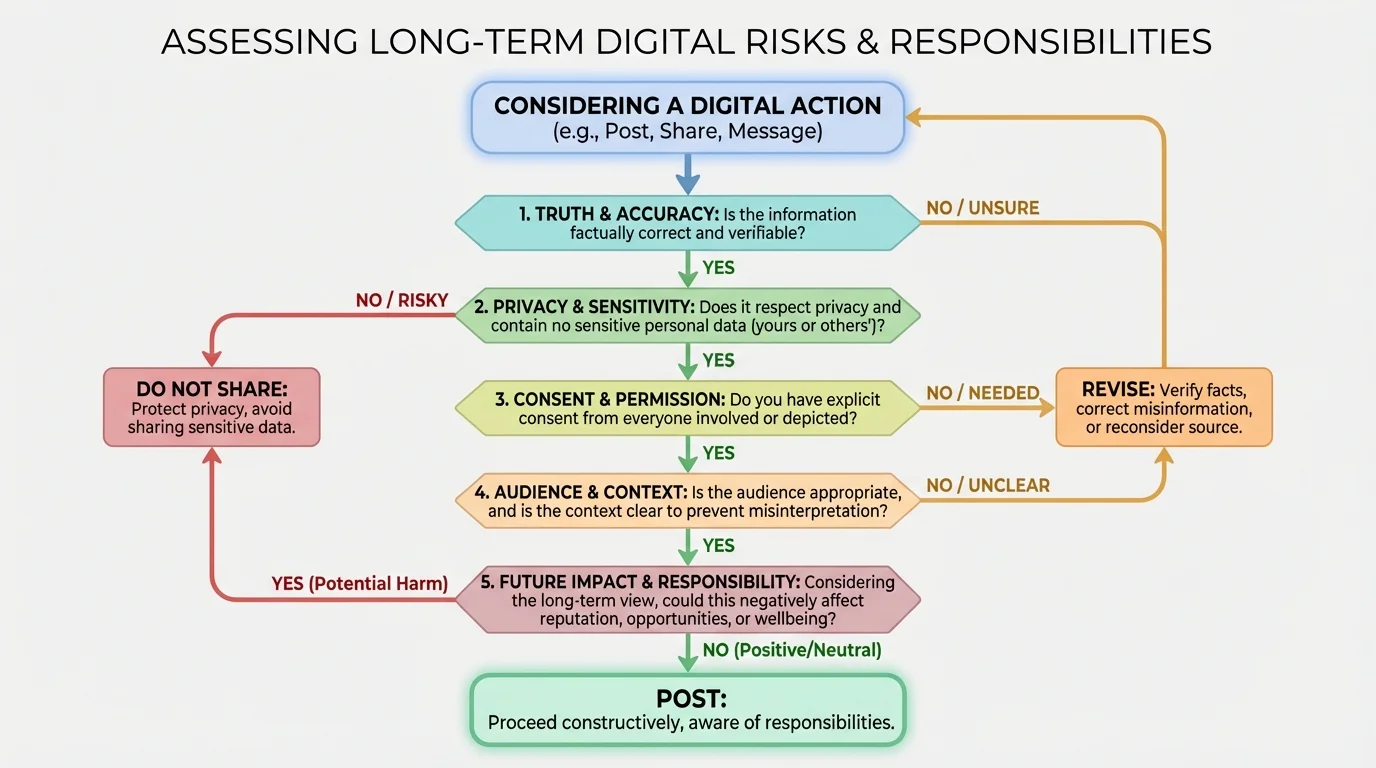
If the answer to any of those questions raises concern, pause. Delaying a post for even ten minutes can save you from a major mistake. If the issue is serious, waiting until the next day is even better. Time helps you separate what feels urgent from what actually matters.
This same framework applies to links and downloads. Before clicking, ask: Do I know the sender? Was I expecting this file? Is the web address normal? Is the message trying to scare or rush me? Many scams succeed because people react before they verify.
Search engines, archived pages, screenshots, and reposts can keep content visible long after the original post is deleted. Deleting is still useful, but it is not the same as undoing.
Risk assessment also applies to group chats and private servers. People often feel safer in small digital spaces, but privacy in groups is fragile. Members can screenshot, forward, leak, or leave and take content with them. "Private" often means "less public," not truly secure.
Being responsible online is not only about protecting yourself. It is also about how your choices affect other people. In community life, that includes clubs, volunteer groups, faith communities, gaming spaces, neighborhood networks, social causes, and local events. Your words can build trust or damage it.
One core responsibility is verifying information before sharing it. misinformation spreads fast because it often triggers strong feelings. A dramatic rumor, edited clip, or fake claim may get more attention than a boring truth. But sharing false information can hurt reputations, create panic, or push people into bad decisions.
Another responsibility is consent. You should not post photos, screenshots, voice recordings, or personal details about others without permission, especially when the content is sensitive or embarrassing. Respecting consent online shows maturity and protects relationships.
Harassment is also a digital citizenship issue. Piling onto someone in comments, mocking someone in a server, reposting private material, or encouraging others to target a person can cause real emotional harm. Sometimes people excuse this as "just online," but the effects are not just online. Stress, fear, sleep problems, isolation, and damaged reputation are real consequences.
| Situation | Irresponsible choice | Responsible choice |
|---|---|---|
| A rumor spreads in a community group | Repost it immediately | Check the source before sharing |
| A friend sends an embarrassing screenshot | Forward it for laughs | Delete it and discourage sharing |
| You disagree with someone publicly | Insult them personally | Respond to the idea, not the person |
| You see a scam post | Ignore it if it does not affect you | Report it and warn others carefully |
| You are added to a heated group chat | Join the attack | Step back or redirect the conversation |
Table 1. Examples of irresponsible and responsible digital choices in community settings.
Responsible community behavior also means knowing when to report harm. If someone is being threatened, impersonated, blackmailed, doxxed, or targeted, silence can make the problem worse. Reporting content, blocking accounts, saving evidence, and contacting a trusted adult or organization leader are practical ways to respond.
Later in life, this matters in workplaces too. Employers expect people to communicate respectfully, protect confidential information, and avoid creating hostile environments online. The habits you build now carry into adult spaces.
Even careful people make mistakes online. Maybe you posted while angry, clicked a suspicious link, trusted the wrong person, or shared something private without thinking it through. What matters next is how quickly and responsibly you respond.
First, contain the problem. Delete the post if that reduces exposure. Log out of other sessions if your account may be compromised. Change passwords. Turn on multifactor authentication. Revoke app access you do not recognize. If money or identity information is involved, contact the company or bank immediately.
Second, document what happened. Take screenshots of threats, scams, fake accounts, or harassment before reporting. If a platform removes content later, you may still need evidence. Keep records of usernames, dates, and messages.
Third, address the human impact. If you hurt someone, a real apology matters. That usually means taking responsibility without excuses, removing harmful content, and changing your behavior. "I was joking" or "everyone does it" is not accountability. Accountability means you understand the effect, not just your intention.
Repair plan after a bad post
Step 1: Remove what you can.
Delete the post, story, comment, or repost. Ask others not to keep sharing it.
Step 2: Contact affected people directly.
Offer a clear apology, especially if privacy, consent, or respect was violated.
Step 3: Review the cause.
Were you angry, trying to impress people, copying others, or ignoring privacy settings? Fix the pattern, not only the single incident.
Step 4: Protect yourself going forward.
Adjust privacy settings, leave harmful group spaces, and set personal rules about what you will not post.
Rebuilding trust takes longer than damaging it. That is true in friendships, jobs, and community groups. But people do recover from digital mistakes when they respond honestly, make changes, and stop repeating the behavior.
Your online presence is part record, part reputation, and part portfolio. As [Figure 4] illustrates, the difference between a risky digital footprint and a strong one often comes down to everyday habits: what you post, how you comment, what you make public, and how intentionally you manage your accounts.
A good digital reputation does not mean being perfect or performing a fake personality. It means your public presence matches the kind of person others can trust. That includes respectful communication, clear boundaries, accurate sharing, and responsible privacy habits.
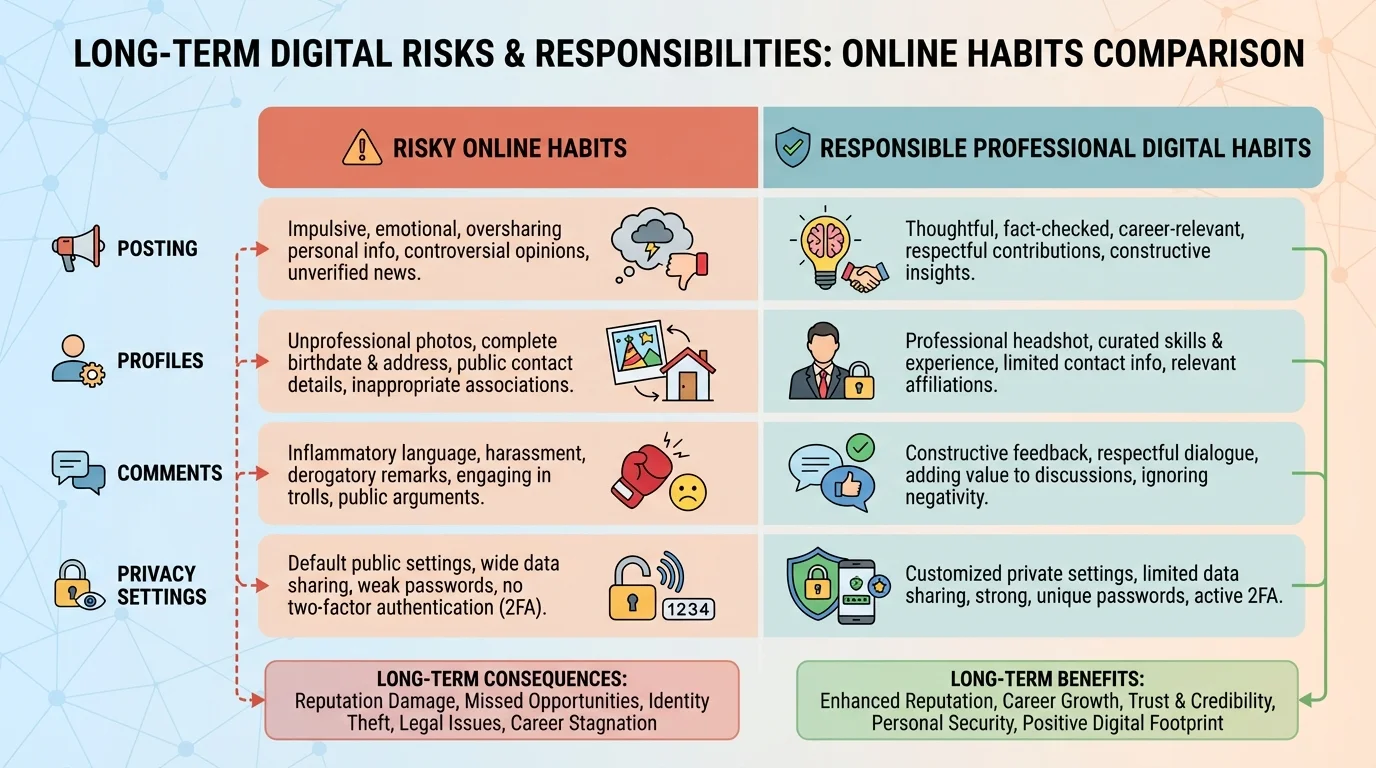
Here are practical ways to build that reputation:
Clean up public profiles. Review bios, profile photos, usernames, old posts, and public comments.
Create positive evidence. Share projects, interests, volunteer work, achievements, creative work, or thoughtful ideas.
Separate audiences. Use privacy settings and, when appropriate, separate professional-facing accounts from private social spaces.
Be consistent. If you want to be seen as dependable, your messages, comments, and behavior should support that image over time.
Set personal standards. Decide in advance what you will never post: private arguments, humiliating content, confidential information, slurs, threats, or posts made while highly emotional.
One useful monthly habit is a personal digital check. Search your name. Review tagged content. Update passwords if needed. Remove old posts that no longer reflect who you are. Check app permissions. Ask yourself whether your public presence supports your next goal, whether that is a job, application, training program, side business, or leadership role. Looking back at the spread effect shown in [Figure 1], this habit helps you act before small issues grow into larger ones.
"Post as if your future self will have to explain it."
This mindset is not about fear. It is about ownership. Your digital life is one of the first places where adult responsibility becomes visible. The choices you make online affect safety, trust, opportunity, and community. That is why strong digital citizenship is a life skill, not just a technology skill.
When you protect your privacy, verify before sharing, respect consent, secure your accounts, and think beyond the moment, you are doing more than avoiding problems. You are building a reputation that can travel with you into work, education, and the communities you care about. The layered security habits described earlier, as seen in [Figure 2], and the pause-check-share decision path from [Figure 3] both support that long-term goal.