A stolen password can empty a bank account faster than many people can finish lunch. That sounds dramatic, but it reflects a real problem: personal and financial information has become one of the most valuable targets in modern life. Teenagers are not "too young" to be affected. Students use banking apps, shopping sites, school portals, payment platforms, job websites, and social media. Each of those spaces can hold information that criminals want.
Protecting information is not just about fear. It is about making careful, systematic decisions. Good personal financial literacy includes knowing how to gather reliable information, recognize risk, and act in ways that support your values and goals. If your goal is financial stability, privacy, or independence, then protecting your identity and accounts is part of reaching that goal.
When someone gains access to sensitive data, the damage can spread quickly. A criminal may use one stolen password to access email, reset other logins, and then reach bank accounts or payment apps. They might open new accounts in someone else's name, make unauthorized purchases, or sell data online. The problem is not only the money lost in the moment. Victims can spend months fixing credit reports, disputing charges, replacing documents, and restoring trust in their accounts.
Information protection also matters because your choices affect other people. If your school account is hacked, your contacts may receive scam messages. If you store a family member's card number insecurely, their money is at risk too. Financial decisions happen in a community context. Responsible habits help protect not only yourself, but also your household and wider network.
Personal information includes details that identify you, such as your full name, date of birth, address, phone number, email, student ID, or Social Security number.
Financial information includes bank account numbers, debit and credit card numbers, PINs, account login details, income records, tax documents, and transaction history.
Identity theft happens when someone uses another person's information without permission, often to steal money, open accounts, or commit fraud.
Not all information is equally sensitive, but students should treat certain details as high-risk. A username by itself may not seem dangerous. Combined with a password, date of birth, or security question answer, it becomes much more powerful. Criminals often build a complete profile from small pieces collected across many places.
Your identity theft risk increases when important details are easy to find, copy, or guess. Some examples are obvious, such as a debit card number. Others are less obvious, such as photos of paperwork in the background of a social media post, screenshots that show account balances, or a casual post announcing your birthday, school mascot, and pet's name. Those details can help someone answer security questions.
Sensitive information can appear in digital and physical forms. Digital forms include emails, cloud storage files, banking apps, shopping accounts, saved payment methods, and text messages containing verification codes. Physical forms include bank statements, pay stubs, insurance cards, checks, tax forms, and school or work records. Effective protection requires paying attention to both.
| Type of information | Examples | Why it needs protection |
|---|---|---|
| Identification data | Full name, birth date, address, student ID | Can be used to impersonate you or verify accounts |
| Account credentials | Usernames, passwords, PINs, verification codes | Allow direct account access |
| Payment data | Card numbers, bank account numbers, payment app logins | Can lead to unauthorized purchases or transfers |
| Financial records | Pay stubs, statements, tax forms | Reveal income, account details, and other private data |
| Behavioral information | Location, purchase habits, online activity | Can be used in targeted scams and social engineering |
Table 1. Major categories of personal and financial information and why each one requires protection.
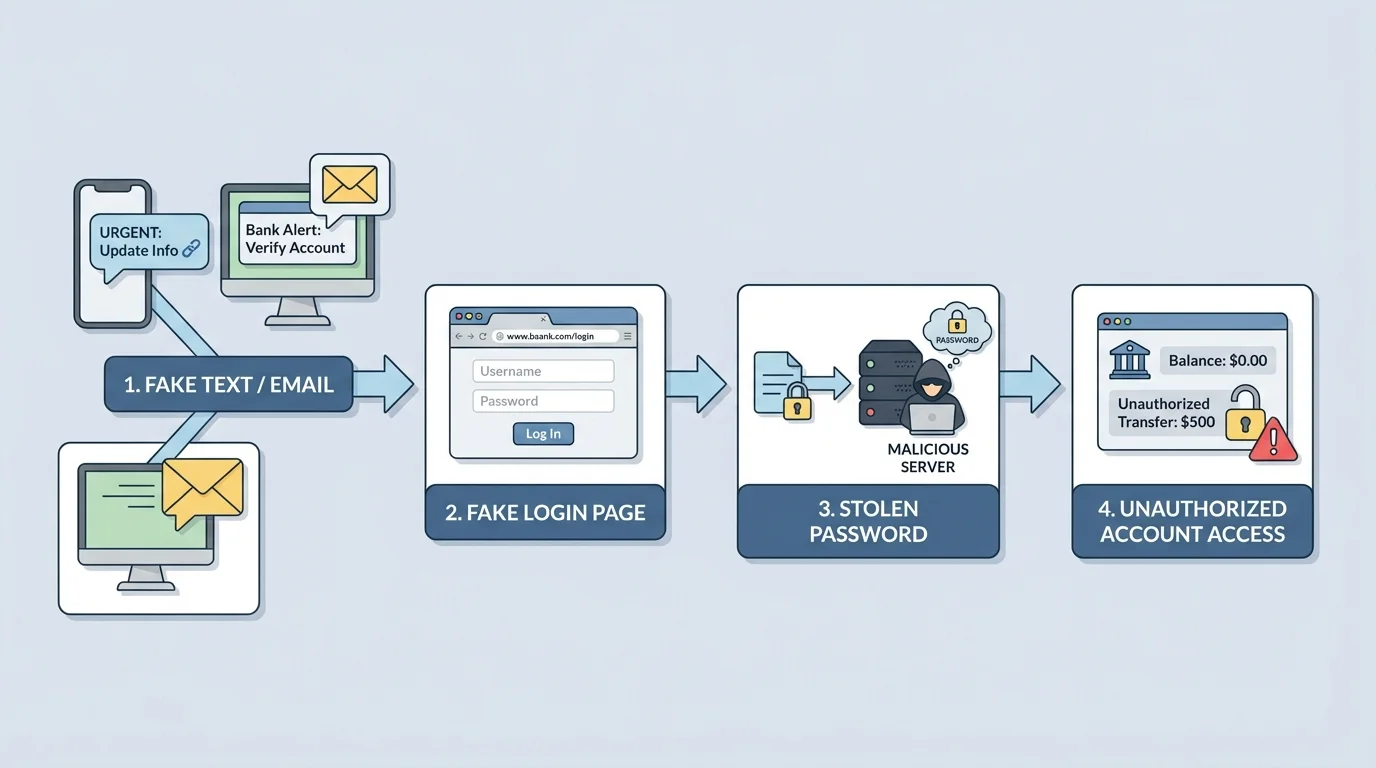
A major danger is phishing, which works through a chain of deception and urgency, as [Figure 1] shows. A scammer pretends to be a trusted source such as a bank, delivery company, school office, employer, or friend. The message may say there is a problem that needs immediate action: "Your account is locked," "Your package is delayed," or "Click now to confirm payment." The goal is to push you into reacting before you think carefully.
Phishing appears in many forms. Email phishing uses fake emails. Smishing uses text messages. Voice phishing uses phone calls. In each case, the attacker may direct a victim to a fake website designed to capture login information or payment details. They may also attach infected files that install malware on a device.
Another threat is social engineering, the practice of manipulating people into giving away information. This can happen online or in person. Someone might pretend to be tech support, ask to "verify" your identity, or use information from your social media accounts to sound believable. Public posts can help criminals learn your routines, interests, school, workplace, and family connections.
Technology creates additional risks. Public Wi-Fi in coffee shops, airports, or stores may be less secure than your home network. Shared computers may save usernames or passwords without your knowledge. Devices that are not updated can have security weaknesses. Fake shopping websites may copy the appearance of real businesses but exist only to collect card numbers.
Notice that many scams depend less on advanced technology than on human behavior. Curiosity, fear, embarrassment, greed, and hurry can all weaken judgment. That is why protecting information involves habits of thinking, not just technical tools. The pattern in [Figure 1] remains the same across many scams: create pressure, gain trust, collect information, and then use it for profit.
Many successful scams contain small mistakes such as odd grammar, unusual web addresses, or requests for secrecy. Scammers often rely on speed and emotion because careful reading makes their tricks easier to spot.
Oversharing can also create danger without any obvious scam. Posting a photo of a concert ticket may reveal a barcode. Showing a new debit card in a celebration post may expose part of the number. Sharing travel plans publicly can tell others when you are away from home. Good security often looks ordinary: not posting too much, not clicking too fast, and not trusting every message that looks official.
The best protection works in layers, as [Figure 2] illustrates. One good habit helps, but several combined habits are much stronger. If one layer fails, another can still stop the attack. Think of security the way you think of sports defense or layers of clothing in cold weather: one barrier helps, but multiple barriers work better.
The first layer is a strong password or, even better, a long passphrase. A passphrase is usually easier to remember and harder to guess because it uses several unrelated words. Avoid using birthdays, pet names, school names, or simple patterns. Most importantly, do not reuse the same password across multiple accounts. If one site is breached, reused credentials can unlock many others.
The second layer is multi-factor authentication, often shortened to MFA. MFA requires at least two forms of proof to log in, such as something you know (a password), something you have (a phone or authentication app), or something you are (a fingerprint or face scan). If a criminal steals a password but cannot access the second factor, the account is still better protected.
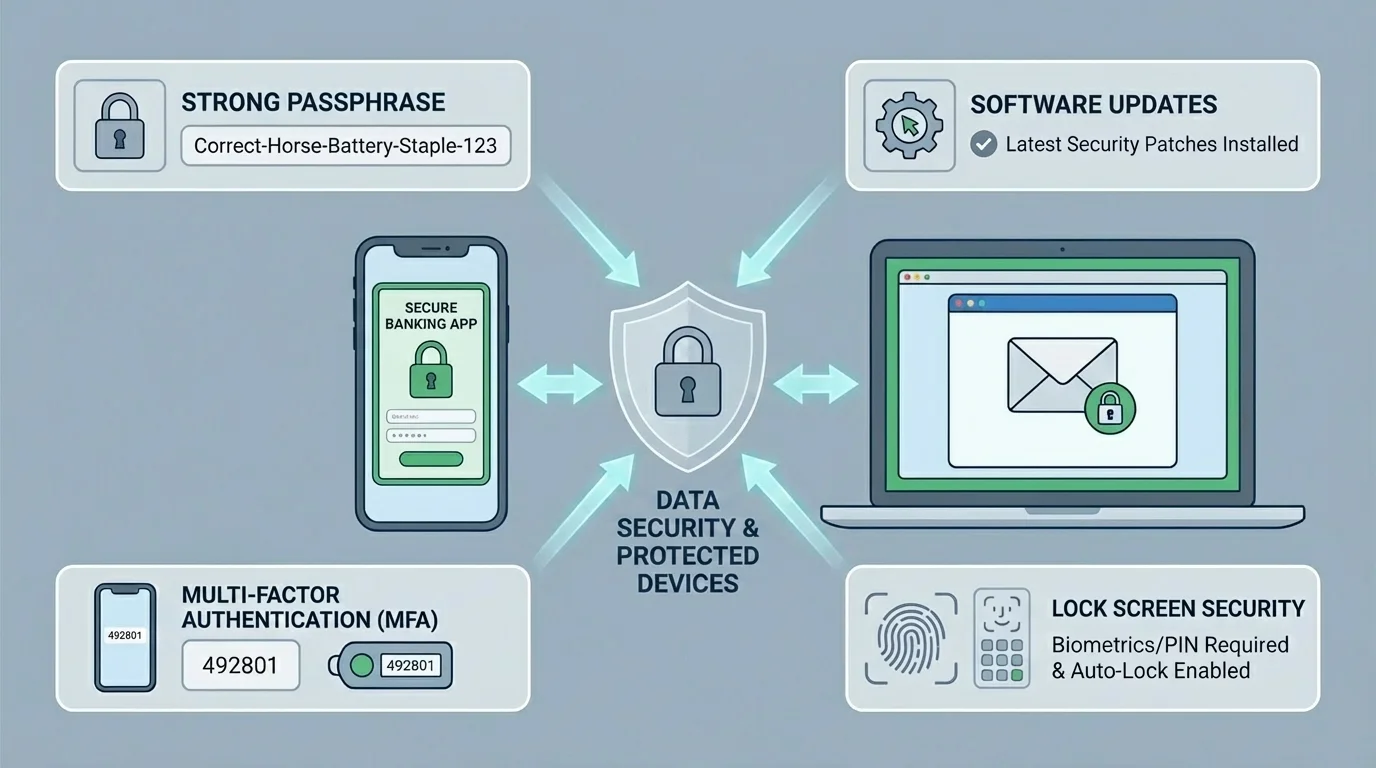
Another essential layer is keeping devices and apps updated. Software updates often fix security flaws that criminals already know how to exploit. Delaying updates may leave a device exposed. Lock screens, biometric access, and automatic timeouts also matter, especially if a phone is lost or stolen.
Privacy settings are part of defense too. Review who can see your posts, contact you, tag you, or find your profile through search. Limit what apps can access, especially location, contacts, camera, microphone, and financial data. If a free app requests more information than it needs, that is a warning sign.
Secure networks matter as well. At home, use a protected Wi-Fi network with a strong router password. On public Wi-Fi, avoid entering bank passwords or payment information unless you are certain the connection is secure. Logging out after use, especially on shared devices, is a basic but important habit. The layered approach shown in [Figure 2] is effective because it does not depend on one perfect decision every time.
Layered security means combining several protective strategies so that one mistake does not cause total failure. A strong passphrase, MFA, updated software, careful privacy settings, and secure browsing work together. In personal finance, this reduces the chance that a single stolen password turns into a major financial loss.
Password managers can also help. They store complex passwords securely and reduce the temptation to reuse easy ones. Students should still protect the password manager itself with a strong master password and MFA. Convenience is useful, but only if it is built on secure habits.
Protecting financial information is not only a digital issue. It includes how you use cards, store documents, track accounts, and respond to unusual activity. Review transactions often. If you know what your normal spending looks like, it is easier to spot fraud quickly. Small unauthorized charges sometimes appear first because criminals test whether a card works before making larger purchases.
It is also important to understand the difference between tools. Debit cards pull money directly from a bank account, while credit cards use borrowed funds that are later repaid. Both require careful use, but unauthorized debit activity can affect available cash immediately. That can be a serious problem if you need money for transportation, food, or bills.
| Habit | Safer practice | Risky practice |
|---|---|---|
| Online shopping | Use well-known sites and verify the web address | Buying from links in random messages |
| Card storage | Keep cards in a secure place and report loss quickly | Leaving cards loose in a backpack or car |
| Account monitoring | Check statements and alerts regularly | Ignoring notifications or never reviewing activity |
| Document handling | Shred sensitive papers before disposal | Throwing statements or forms away intact |
| Peer-to-peer payments | Send only to verified people and double-check usernames | Paying unknown sellers with no buyer protection |
Table 2. Everyday financial habits that reduce or increase risk.
Paper documents deserve attention too. Store tax records, checks, identification documents, and bank documents in a secure location. If a document is no longer needed, shred it rather than throwing it away whole. Mail theft, stolen wallets, and lost backpacks can all expose information in ways that have nothing to do with hacking.
Case study: spotting suspicious account activity
A student checks a payment app and sees three transfers: $12, $48, and $310. Only the first transaction is familiar.
Step 1: Compare the transactions with known purchases.
The student confirms that only the $12 payment matches a real purchase.
Step 2: Estimate the unauthorized total.
The suspicious amount is $48 plus $310, so the loss is \(48 + 310 = 358\).
Step 3: Act quickly.
The student changes the password, signs out of other devices, contacts the payment service, and informs the linked bank.
Fast action matters because the unauthorized total is $358, and delay may allow more transfers.
Budgeting tools and finance apps can be useful, but students should choose them carefully. Read privacy policies, understand what data the app collects, and find out whether account information is encrypted and whether the company shares data with third parties. A convenient app is not automatically a safe app.
One of the most powerful financial skills is learning not to act on the first message you see. Scammers want quick, emotional decisions. Reliable decision-making means pausing, checking, and confirming. If a bank text says your account is frozen, do not click the link immediately. Open the official app yourself or call the number on the back of the card. Go to the source independently.
This habit reflects a larger principle in personal financial literacy: use reliable information to make systematic decisions. "Systematic" means you follow a process rather than guessing. For example, if you receive an urgent message asking for payment, you might use this sequence: identify the sender, verify the web address, compare the claim with official account information, contact the institution through a trusted channel, and decide only after confirmation.
Warning signs include urgent threats, requests for secrecy, pressure to act immediately, offers that sound too good to be true, unusual payment methods, poor spelling, and links that do not match the claimed business. A real organization may contact you, but legitimate institutions usually do not ask for full passwords, PINs, or verification codes through random messages.
Reliable sources are ones you can verify independently. A message about your account is not trustworthy simply because it uses a bank logo or official-looking language. Trust should come from confirmation through a known website, app, phone number, or in-person office.
Values also matter here. Some people value convenience most; others value privacy more strongly. Community and family experiences may shape what risks feel acceptable. But regardless of personal values, a good strategy should be informed, deliberate, and realistic. Choosing convenience without understanding risk is not a strong financial decision.
Even careful people can be targeted, so it is important to know how to respond. Fast, organized action reduces harm, as [Figure 3] demonstrates. If you think an account has been compromised, start by changing the password immediately and signing out of all other sessions if that option exists. If the same password was used elsewhere, change those accounts too.
Next, contact the bank, card issuer, payment platform, or affected company. Ask them to lock the account, reverse fraudulent charges if possible, and monitor for suspicious activity. Save screenshots, email records, and transaction details. Documentation helps when disputes must be filed or fraud must be reported.
If highly sensitive information such as a Social Security number has been exposed, a credit freeze may be appropriate. A credit freeze restricts access to your credit report, making it harder for someone to open new credit in your name. You should also review your credit report for accounts or inquiries you do not recognize.
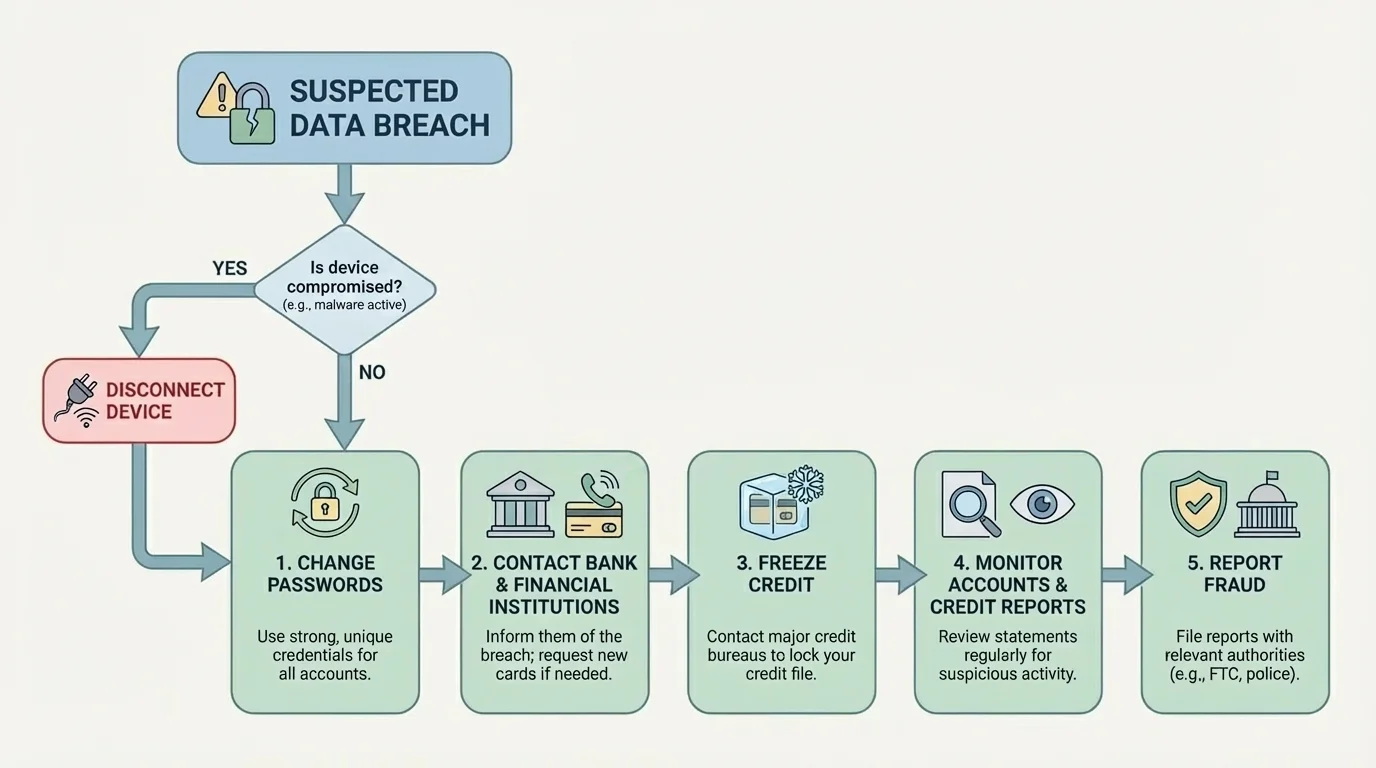
In some cases, devices should be scanned for malware or reset. If you clicked a suspicious link or downloaded a dangerous file, disconnecting from the internet and getting technical help may be wise. At school or work, report the problem to the appropriate technology or administrative office if their systems may be affected.
Victims sometimes feel embarrassed, which leads them to delay reporting. That delay can make things worse. Scams are designed to trick people. The response process in [Figure 3] matters more than blame. Protect the account, alert the institution, document the evidence, and keep monitoring.
"Trust, but verify."
— A useful principle for digital and financial safety
Families and communities can support this process. A student may need help contacting a bank, replacing identification, or reviewing a credit report. Asking for help is a responsible decision, not a weakness. Financial protection often works best when people communicate clearly and act quickly together.
These strategies apply to ordinary situations: applying for a job, buying concert tickets, joining a school club, using gaming platforms, signing up for scholarships, or ordering food online. Any time you are asked for information, ask three questions: What is being requested? Why is it needed? How will it be protected?
At school, be careful with shared devices, saved logins, and links sent through messages or group chats. At work, protect payroll information and direct deposit details. In social media and gaming spaces, be skeptical of strangers asking to trade items, send money, or "verify" your account. In online shopping, check for secure payment practices, realistic prices, and a legitimate return policy.
Good protection is not paranoia. It is disciplined judgment. You do not need to assume every message is fake, but you should assume every request deserves evaluation. That mindset supports long-term goals such as financial independence, trustworthiness, and responsible participation in your community.
As you make decisions about privacy and money, remember that protecting information is part of protecting opportunity. A secure account, a careful click, or a verified source may seem like a small choice today, but those small choices build a much stronger financial future over time.