A single message can change the tone of your whole day: "Send one picture or I'll post that screenshot," "If you cared about me, you would," or "Don't tell anyone." Online pressure often moves fast, and that speed is part of the danger. When someone uses guilt, fear, threats, or humiliation to control you online, the goal is usually not connection. It is control. Knowing how to respond safely can protect your privacy, your mental health, and sometimes your physical safety too.
One important truth comes first: if someone pressures you, tricks you, threatens you, or shares an image without your consent, that is not your fault. Even if you replied, trusted them, flirted, sent something before, or made a choice you now regret, the person causing harm is still responsible for their behavior. Your job now is not to be perfect. Your job is to get safe, protect evidence, and get support.
Digital communication makes it easy for people to contact you late at night, from fake accounts, from gaming chats, through disappearing messages, or by jumping between apps. That can make pressure feel inescapable. A person may act romantic one minute and threatening the next. They may save private content, pretend to know your friends, or claim they will expose you unless you obey. Quick panic reactions can make things harder, so having a plan matters.
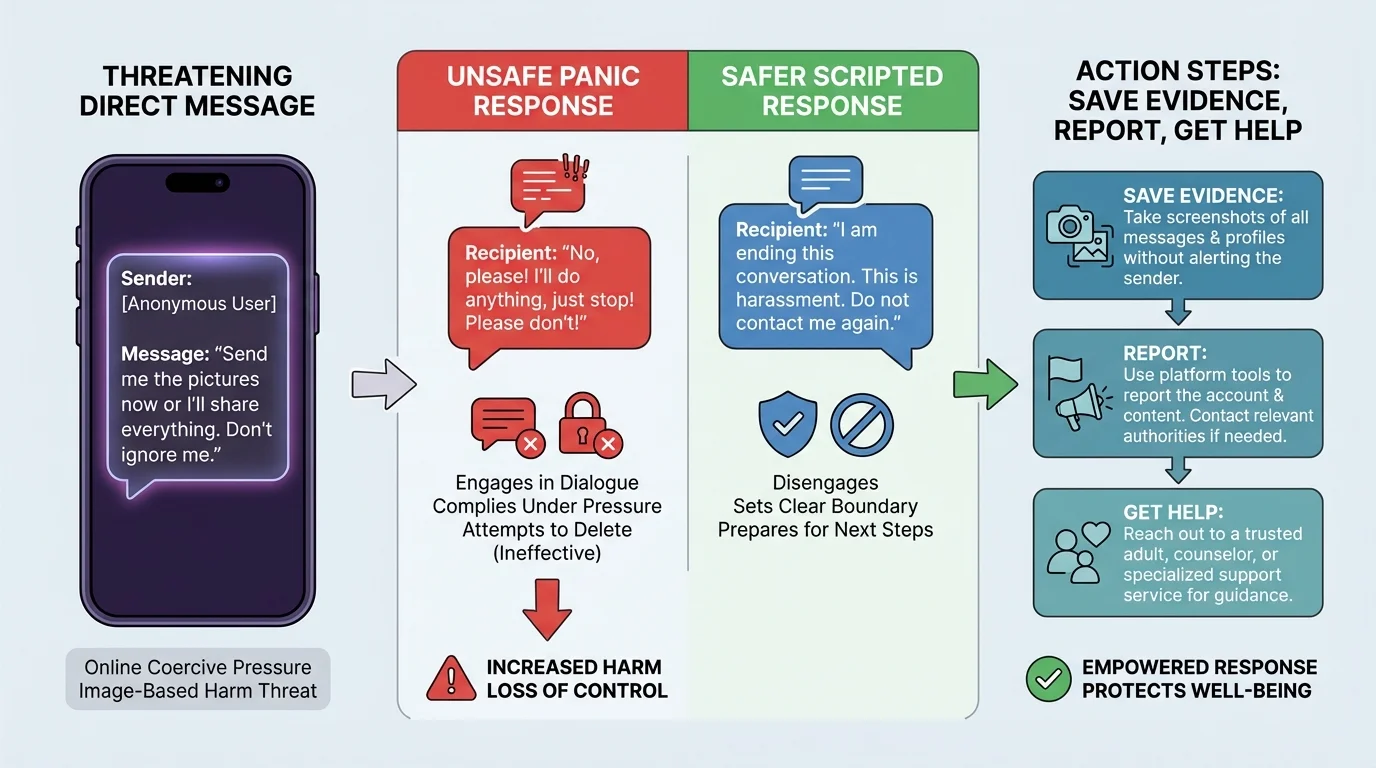
When you respond well, you reduce the other person's power. When you respond in a panic, they often escalate. That does not mean you cause the harm. It means strategy matters. The safest response is usually calm, brief, evidence-focused, and supported by adults or professionals when needed.
Online coercive pressure is when someone tries to control your choices online using threats, guilt, manipulation, intimidation, blackmail, or repeated pressure.
Image-based harm is harm involving photos, videos, screenshots, or edited images, including sharing private images without consent, threatening to share them, or using fake images to humiliate or control someone.
Sextortion is a form of exploitation where someone threatens to share sexual images or information unless the target sends more content, pays money, or follows demands.
These situations can happen in direct messages, group chats, dating apps, gaming platforms, text messages, or social media. They can involve someone you know, someone you met online, an ex, a stranger using a fake profile, or even a scammer pretending to be your age.
Coercion online rarely starts with a dramatic threat. As [Figure 1] shows, it often builds through tactics like flattery, secrecy, fake urgency, guilt, and then pressure. A person may say, "You can trust me," "Everyone does this," "Prove you love me," or "If you stop responding, I'll send this to people." The pattern matters more than the exact words.
Watch for red flags: someone pushing for private images quickly, refusing to respect "no," asking you to hide the conversation, threatening self-harm to control you, demanding passwords, claiming they will ruin your reputation, or using screenshots as leverage. Another warning sign is when the person keeps moving the goalposts. If you send one thing, they demand more. If you apologize, they still threaten. That is how manipulation works.
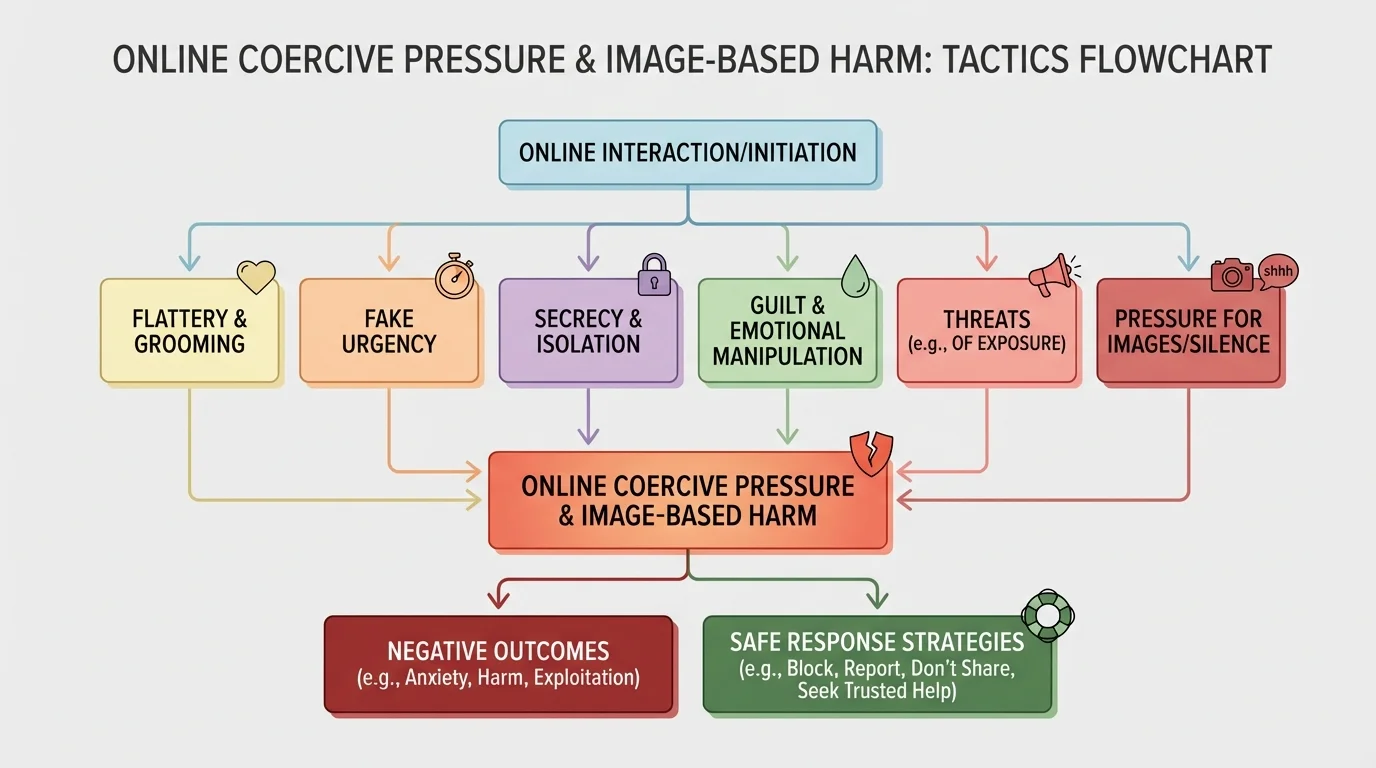
Image-based harm also includes nonconsensual sharing, recording without permission, edited or fake sexual images, and reposting private content after a breakup. Some people assume harm only qualifies as harm if a sexual image was originally real. That is false. A fake image used to humiliate or threaten you is still harmful and should still be reported and addressed seriously.
A useful term here is consent. Consent means a clear, voluntary, ongoing agreement. If someone shares, pressures, records, or posts without your permission, there is no consent. If they keep pressuring after you say no, there is no consent. If they use fear or guilt to get agreement, that agreement is not freely given.
Many people who use online pressure are testing whether panic will make you easier to control. A calm pause, evidence collection, and quick support from an adult can interrupt that pattern fast.
Sometimes the person harming you says things like "This will ruin your life if you tell anyone." Secrecy is one of their strongest tools. The more isolated you feel, the more power they have. Breaking secrecy safely is often the turning point.
When you are under pressure, your brain may want to fix the problem immediately. But fast reactions can create more risk. A simple plan helps you slow down and act in the right order: pause, protect, preserve, report, and reach out.
Step 1: Pause and breathe. Do not send more images, money, passwords, or personal details. Do not agree to meet up. Do not try to "negotiate" your way out by giving them something else. In many cases, giving in once leads to more demands, not less.
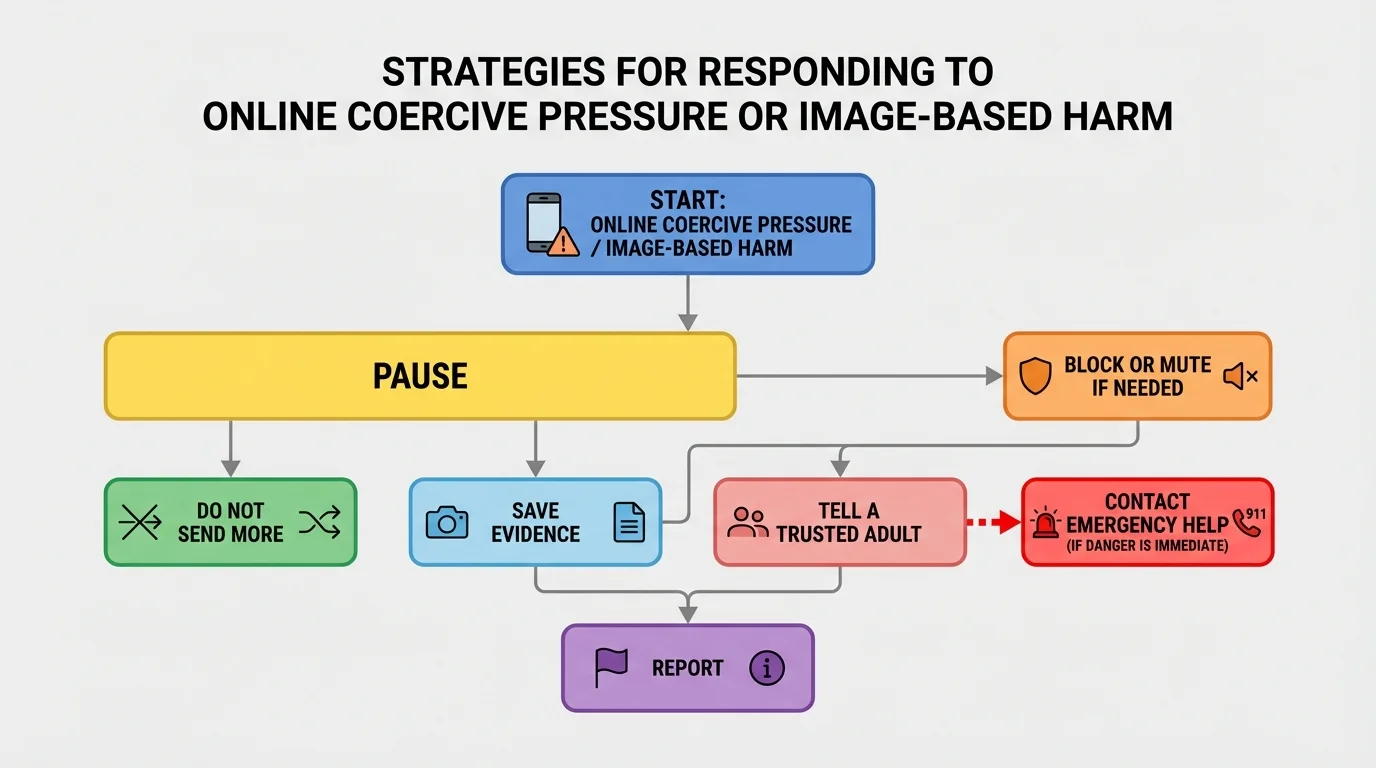
Step 2: Stop the flow of new content. If the person is demanding images, stop sending anything. If they are calling repeatedly, do not answer just because they are persistent. If they are asking you to delete the chat, do not do that yet.
Step 3: Save evidence. Take screenshots of usernames, profile links, messages, threats, payment requests, timestamps, and any shared images or posts. If the platform shows disappearing messages, capture what you can as soon as possible. Save URLs if available. Evidence helps adults, platforms, and law enforcement understand what happened.
Step 4: Tell a trusted adult quickly. This might be a parent, guardian, older sibling, school counselor, coach, club leader, or another safe adult. If saying it out loud feels hard, send a short message: "Someone is threatening me online with images/screenshots. I need help now. Please stay calm and help me report it."
Step 5: Use platform safety tools. Report the account, the messages, and any harmful image-sharing. Many platforms have options for harassment, blackmail, impersonation, and nonconsensual intimate imagery. Reporting creates a record and may lead to removal or account suspension.
Step 6: Block when blocking is safe. In many situations, blocking helps stop contact after evidence is saved. But if an adult or law enforcement asks you to wait briefly to document more information, follow that guidance. Safety comes first.
Step 7: Get emergency help if there is immediate danger. If the person knows where you live, is threatening to come to your home, is threatening violence, or is saying they will harm you or someone else right now, contact emergency services and tell an adult immediately.
Why "do not send more" is so important
People using sextortion or coercive pressure often promise that one more image, one payment, or one apology will end the problem. In reality, compliance often confirms that fear is working. That can lead to more demands. Refusing to continue, while saving evidence and getting help, cuts off the cycle more effectively.
You may still choose to send a single brief message before blocking if an adult helping you agrees and if the message does not increase risk. Keep it short and non-emotional: "Do not contact me again. I am saving this conversation and reporting it." Then stop engaging. You do not need to argue, explain, or prove anything.
[Figure 3] Evidence is most useful when it shows the full picture: who contacted you, what they said, when they said it, and what account they used. Useful evidence includes screenshots, usernames, timestamps, links, and records of reports. Do not edit screenshots or crop out identifying details unless you are making a safer copy to share with a trusted adult.
After evidence is saved, secure your accounts. Change passwords for email, social media, gaming, and any account the person might know about. Use strong, unique passwords and turn on two-factor authentication when available. Review privacy settings, remove unknown linked devices, and check whether your location sharing is turned on anywhere.
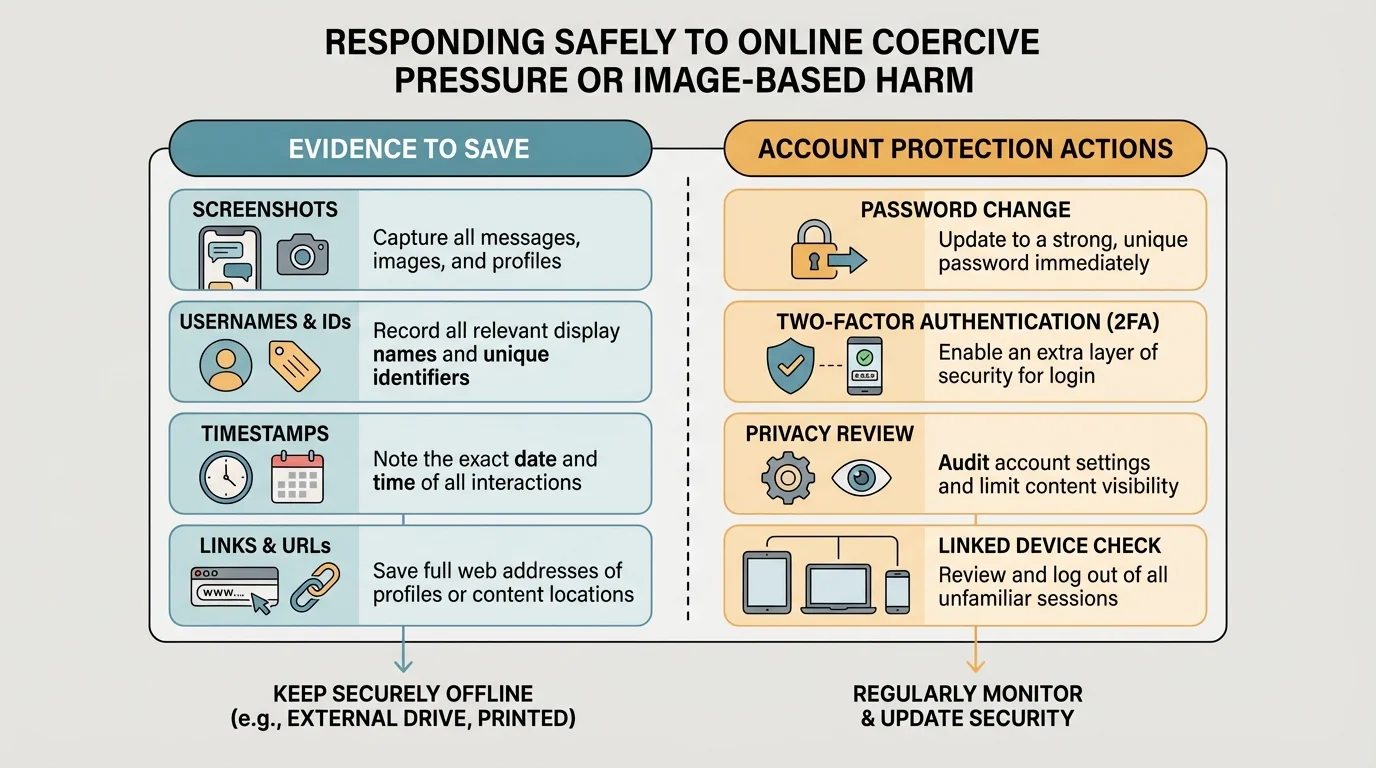
If an image has already been posted, act fast but strategically. Report the content on the platform. Ask a trusted adult to help document the post before removal by saving the link and screenshots. In some places, laws and platform policies can support takedown requests for nonconsensual sexual content or exploitation. If you are a minor, adults should help with any law-enforcement contact.
If someone hacks, impersonates, or creates a fake account in your name, report impersonation separately from harassment. Save proof that the account is fake, such as mismatched profile information or messages from people who saw it. Let friends and family know not to engage with the fake account.
As we saw earlier in [Figure 1], manipulative people rely on secrecy and urgency. Account protection slows them down. It also helps you regain a sense of control at a moment when things may feel chaotic.
| Situation | Best immediate action | Avoid |
|---|---|---|
| Threat to share a private image | Save evidence, tell an adult, report, block when safe | Sending more images or money |
| Fake account using your name or photo | Screenshot profile, report impersonation, alert trusted people | Arguing publicly with the account |
| Repeated pressure from someone you know | State no once, save messages, get support, restrict contact | Trying to "keep the peace" by giving in |
| Immediate threat of violence | Contact emergency help and a trusted adult right away | Handling it alone |
Table 1. Quick-response choices for common online coercion and image-based harm situations.
Many young people avoid telling adults because they fear losing phone access, getting blamed, or being judged. Those fears are real, but silence usually gives the harmful person more time and power. A strong adult response should focus on safety rather than punishment.
You do not need a perfect explanation. Try a script like this: "I need help with something serious online. Someone is threatening me or using images/screenshots against me. I have saved evidence. Please help me report it and figure out the next step." This keeps the conversation focused and practical.
What to say when asking for help
Step 1: State the problem clearly.
"Someone online is pressuring or threatening me."
Step 2: Say what kind of help you need.
"I need help saving evidence, reporting it, and staying safe."
Step 3: Mention urgency if needed.
"They know personal information about me," or "I think they might post something soon."
Step 4: Ask the adult to stay calm.
"Please help me solve this without yelling at me right now."
If the first adult does not respond well, tell another one. Keep going until someone takes it seriously. Support can also come from platform safety teams, local crisis lines, and law enforcement in cases involving exploitation, stalking, extortion, or threats of violence.
A related term is digital footprint. Your digital footprint is the trail of information connected to your online activity. In a crisis, your digital footprint can help prove what happened, but it can also reveal details about your routines, accounts, or contacts. That is why privacy settings and evidence collection both matter.
When you are stressed, it helps to have words ready. Scripts reduce panic and help you avoid saying things that give the other person more control. The comparison in [Figure 4] shows how a pressured reaction can differ from a safer one.
Scenario 1: Someone you met online says they will send a screenshot of your private chat to people you know unless you send a photo. A safer response is not to bargain. Save evidence, stop replying, tell an adult, and report the account. If you send more, they may only ask for more again.
Scenario 2: An ex threatens to post an old image after an argument. You might want to argue or insult them back. That usually adds heat, not safety. Better: screenshot the threats, store them somewhere safe, tell a trusted adult, and report any post immediately if it appears.
Scenario 3: A person says, "If you loved me, you'd send me something private. If not, I'll know you never cared." This is emotional manipulation, not respect. A healthy response is: "No. Do not ask again." If they continue, save the messages and limit contact.
Scenario 4: A stranger claims to have hacked your webcam and demands money. This may be a scam, but treat it seriously enough to protect yourself. Do not pay. Save the message, tell an adult, change passwords, run security checks on your device, and report the account. Many scammers bluff using fear.
Safe reply scripts
Script for pressure:
"No. Do not contact me about this again."
Script for threats:
"I am saving this and reporting it."
Script for getting help from a friend:
"I need you to stay with me on chat while I tell an adult."
Later in a similar situation, the pattern from [Figure 4] still applies: short response if needed, no bargaining, save evidence, then move toward support and reporting. The goal is not to win an argument. The goal is to reduce harm.
Prevention is not about blaming people for being targeted. It is about lowering risk and increasing control. Some useful habits are keeping accounts private when possible, limiting what strangers can see, not sharing passwords, turning off location sharing unless necessary, and thinking carefully before storing sensitive images on devices or cloud accounts.
Strong boundaries help too. A boundary is a limit you set to protect your well-being. Online, that might sound like: "I do not send private pictures," "I am not comfortable with that," or "Do not message me late at night." People who respect you may be disappointed sometimes, but they will respect the limit. People who attack your boundary are showing you something important.
"Someone who cares about you will respect your no."
You can also help friends safely. If a friend tells you someone is threatening them, avoid saying, "Why did you send it?" or "Just ignore it" without helping. Instead say, "This is serious. Save everything. Let's tell a trusted adult now." Offer to stay online with them while they report or make the call. Support should reduce shame, not increase it.
If you ever receive someone else's private image, do not forward it, joke about it, save it for later, or post about it. Delete it if appropriate, report it if needed, and do not become part of the harm. Consent applies not only to creating content but to sharing it.
Your safety matters more than your embarrassment. A difficult conversation with a trusted adult is temporary. Exploitation grows when it stays hidden.
One last practical habit: create a personal safety list before you need it. Keep the names of two or three trusted adults, know where reporting tools are on the apps you use most, and make sure your strongest account security is on your email account first. Your email is often the key to everything else.